Cryptology and Systems Security
1. Introduction
1.1 Cryptology's Birth (Antiquity)
1.1.1 Cryptology's Birth (Antiquity)
What is this Cryptography? When we try to hide a message, make it illegible or incomprehensible by unauthorized persons but accessible to authenticated, we can say that we are working on "cryptography".
Cryptology consists of two parts:
The cryptography: Encryption of clear messages.
The cryptanalysis: Deciphering cryptograms (encrypted messages).
Cryptography is born for military and diplomatic reasons.
The first coded document has been found in Iraq. Indeed, a ciphertext
appearing on a clay tablet was engraved by a Babylonian potter who wanted conceal his recipe for more success.
After adding a few consonants and recognized words to the spelling visionary, archaeologists have been able to decipher the formula
manufacturing of varnishes potter jealously guarded the exclusivity.

V ° - II centuries BC:
The Greeks have renovated the cryptography putting a new system available to their powerful army. To understand the system you
must take a stick with well-defined diameter (scytale) used key for encoding, then take a ribbon and wrap the stick with parallel turns.
The message will be written directly on the wound strip, line by line along the length of the stick!
Once done, pull the tape and your message is encoded Hop. To decode it you must use the same key used for encryption,
that is, a stick of the same diameter as that used for coding!
It was not a good system because, to send a coded message from Greece to Rome it was sent with the proper and clear key. It was enough that the stick is stolen by spies so an unauthorized person is able to read the secret message!
Waiting the second century to see a real change in the method; Polybius the Romans improved transmission system that was designed by Kléoxénos and Démokleïtos .
Polybius invented a system of encryption square, it was called "Polybius square". The idea was to put all the letters of the alphabet in a 5x5 table. To encode a letter you had to replace it with its coordinates in the table.
| 1 | 2 | 3 | 4 | 5 | |
| 1 | A | B | C | D | E |
| 2 | F | G | H | I,J | K |
| 3 | L | M | N | O | P |
| 4 | Q | R | S | T | U |
| 5 | V | W | X | Y | Z |
In fact, the complexity of this system naturally protected messages that the Ancients sent any person could see communication as Polybius does not mention that it had to happen out of sight but like any cryptographic method, the observer could not spontaneously make sense of these signals. 50 years BC:
One of the first mathematical algorithms was made by Julius Caesar in order to communicate his orders and relationships with his lieutenants.
The principle is very basic: It is a shift system which involves replacing a letter by the next letter or letter after the 3rd or 4th and so on in the order
of the alphabet. There are many variations to this system.
Exemple : Plaintext = "Bonjour" Ciphertext = "CP OKPV S"By a simple brute attack anyone should be able to break the code, so I can not not advise you to use it to encrypt your messages!
1.2 Should we trust a code?
I'll just explain two historical examples:(a) On October 15, 1586: The Queen of Scots Mary Stuart was accused for treason, accused of having participated in a conspiracy aimed to assassinate the Queen Elizabeth with the goal of sizing herself for the crown of England. Sir Francis Walsingham, First Secretary of Queen Elizabeth, had already stopped the other conspirators had obtained their confessions and killed them. Unfortunately for Mary, Walsingham was also the head of British Intelligence. He intercepted the letters of Mary and the conspirators Thomas Phelippes had successfuly decoded them. The figure used was not simply a substitution, but rather a nomenclator, as shown in the figure below. It consisted of 23 symbols replacing letters of the alphabet (except j, v and w) 36 as well as symbols for words or phrases. There were also four draws and one symbol meaning that the following letter was a doubled letter.
The code by image:
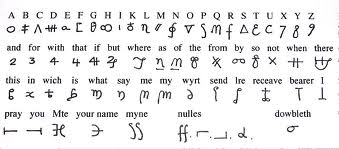
Mary was sure that her code was inviolable and it ended up being broken with a frequency analysis.
(b) Long time ago, before the second World War Enigma machine has emerged, created by a Dutch resident in Germany Dr. Arthur Scherbius . This cryptographical machine was regarded by the Germans as a totally safe and inviolable machine. During the second World War, the Polish secret services were able to grab a copy and gave it to the British. The Germans did not know that the French and Polish services against espionage also worked since 1930 on a decryption method. Commander Gustave Bertrand of the French secret services, recruited for that Hans Thilo Schmidt (whose code name was Asche), who was the same time working for Chiffrierstelle.
Lorsque World War II broke out in 1939, the Allies could decrypt Enigma's messages. July 24, 1939, Marian Rejewski (responsible Biuro Szyfrow - European service in the most advanced research in the German encryption) gave a model of the Enigma's machine to Bertrand and the Commander Alistair Denniston, head of decryption Intelligence Service (IS) British. The German defeat was partly caused by their blind confidence in their machine that has proved not very effective.
1.3 First conclusion
We have seen that the encryption can never be a sure way against attacks. You should never say "My code can never be broken," , avoid the guilt of the Germans because we know now that what is impossible to break today becomes a breeze 2 years later! However there is only one algorithm proved mathematically secure, the Vernam cipher that we will see later.